
When Edward Snowden pulled back the curtain on the world we thought we knew, and revealed the jaw-dropping extent of NSA surveillance on American citizens and people around the globe
Between 2013 and 2015, Ultraculture closely followed Edward Snowden’s revelations of the massive NSA surveillance programs of American citizens.
It’s hard to overstate how epochal of an event this was, particularly for Millennials, and particularly for Internet-focused people. Suddenly, the most paranoid rantings of hippies and conspiracy theorists, going back to the 1960s, seemed positively understated compared to reality.
Moreover, Snowden’s revelations broke the illusions of the Obama era and the narrative that our new Nobel Peace Prize-winning president had America’s best interests in mind. Of course, centrist Democrats and the mass media closed wagons around Obama and came up with 1,001 ways to excuse him; however, for the majority of the world, the spell was broken. The idea that US intelligence agencies would wiretap their entire population, not to mention the rest of the world’s populations, was a totalitarian horror that made both Orwell and the mid-20th century dictators he was writing about seem like amateurs. To suggest that the NSA surveillance scandal helped fuel the populist backlash of the 2016 elections, and the campaigns of both Bernie Sanders and Donald Trump, is probably a safe argument to make.
I’m writing this in 2017, five years after Snowden’s revelations shook the world. In the years following PRISM-gate, it was fascinating and a bit sickening to watch just how quickly things returned to business as usual. Not only was Obama never held responsible for NSA surveillance, but the mass media largely re-absorbed the Snowden scandal and spit it back out in the form of entertainment, as in Oliver Stone’s middling Snowden film, not to mention the much worse Benedict Cumberbatch vehicle The Fifth Estate
, both of which functioned to process very real, ongoing and incredibly dangerous (to the State) events and turn them into fiction. It was an amazing lesson in what Guy DeBord called the Society of the Spectacle
, the grim realization that revolutionary activity is largely impossible in late capitalist societies, because it will inevitably be re-absorbed and re-gurgitated as mass media and Spectacle.
These days, Julian Assange has been re-cast as a villain of the highest order and a pawn of Russian intelligence, primarily because his leaks of John Podesta’s e-mails in 2016 did not serve the interests of American liberals, who were frantically attempting to block the ascendency of Donald Trump. This, for me, proves that the American liberal power bloc was never concerned about truth, justice or the preservation of the American way. What they were and are truly concerned about is the great game of partisan politics—and unlike both the Snowdens and Assanges of the world, and most Internet-savvy Millennials, the DNC assumes that the rest of the world believes in that game, too.
But that is their karma to deal with, and if American liberalism is to survive Trump and the global rise of nationalism (as well as new far-left parties), it will need to reform itself in a new vehicle capable of handling reality as it is.
Preserved below is Ultraculture’s coverage of Snowden’s NSA surveillance revelations, and the ongoing national meltdown over NSA surveillance and the loss of online privacy, so that it can be read in one place, and so future readers can understand how we were reacting in real time to a truly disturbing moment. Even if you think you know the full history of what happened, there’s sure to be fresh revelations inside.
I have preserved tense and timelines in these articles so that they can be read as they were while events were happening.
PRISM-Gate: When America Finally Woke Up to NSA Surveillance (6/7/2013)

On Wednesday, Glenn Greenwald at the Guardian published an article revealing that the Obama administration is collecting metadata (that is, information about calls, not the calls themselves) from Verizon’s entire customer base. The article reads:
The National Security Agency is currently collecting the telephone records of millions of US customers of Verizon, one of America’s largest telecoms providers, under a top secret court order issued in April.
The order, a copy of which has been obtained by the Guardian, requires Verizon on an “ongoing, daily basis” to give the NSA information on all telephone calls in its systems, both within the US and between the US and other countries.
The document shows for the first time that under the Obama administration the communication records of millions of US citizens are being collected indiscriminately and in bulk – regardless of whether they are suspected of any wrongdoing.
The secret Foreign Intelligence Surveillance Court (Fisa) granted the order to the FBI on April 25, giving the government unlimited authority to obtain the data for a specified three-month period ending on July 19.
On Thursday, Greenwald widened the scope of the story, revealing that the NSA now has a (previously undisclosed) program dubbed PRISM, which allows the agency direct access to the systems of Apple, Facebook, Google, Microsoft, AOL, Skype, Yahoo and others—giving them instant access to search histories, e-mails, file transfers and chat logs directly from these companies’ servers. Google and Apple have both disavowed knowledge of the program.
The National Security Agency has obtained direct access to the systems of Google, Facebook, Apple and other US internet giants, according to a top secret document obtained by the Guardian.
The NSA access is part of a previously undisclosed program called PRISM, which allows officials to collect material including search history, the content of emails, file transfers and live chats, the document says.
The Guardian has verified the authenticity of the document, a 41-slide PowerPoint presentation – classified as top secret with no distribution to foreign allies – which was apparently used to train intelligence operatives on the capabilities of the program. The document claims “collection directly from the servers” of major US service providers.
The most shocking thing about this to me is that people are shocked at all. Anybody with their eyes even a millimeter open has seen this coming since the first PATRIOT Act was passed in 2001. It’s been obvious what they’ve wanted all along, and anybody who’s followed the increasing encroachment of government surveillance over the last decade and more will have already assumed total information awareness was the case. Obama’s major achievement has been the mass acceptance of Bush policies that were once deemed shocking and appalling. (In fact, it turns out that James Comey, Obama’s current pick to head the FBI, authorized Bush’s initial illegal NSA wiretapping plan in 2005.)
It won’t be a surprise that Internet and phone data are monitored. It won’t be a surprise that all of this information is immediately recorded and housed in underground bunkers. It won’t even be a surprise that Americans have been gradually herded into centralizing their data on a few platforms—Verizon, Facebook, Apple, Google and others—that have open backdoors to the federal government. We’ve known that Facebook has an open door policy on sharing users’ data with the government, without even needing the formality of a subpoena, for years.
RELATED: 9 Tools for Private Browsing That Will Keep You Safe From Hackers, the NSA and Prying Eyes
Such surveillance policies will only be the tip of the iceberg. We haven’t even begun to consider surveillance satellites, for instance. (MIT, by the way, has just demonstrated an “invisibility cloak” that could be used to hide satellites.) What we don’t know can hurt us, and if Wednesday’s revelations are anything to go on, we don’t even know what we don’t know. We can only suspect what we don’t know. And what we can suspect is what we’ve suspected all along: that everything is recorded and monitored.
The Atlantic reports on the vast, terrifying unknown that is the Obama administration’s surveillance policies—increasingly unknown because Obama has more ruthlessly enforced secrecy and, in tandem, more viciously attacked whistle-blowers than any previous president. (PFC Bradley Manning, who was kept in subhuman conditions for years and potentially tortured for leaking material to Julian Assange, including video of US soldiers murdering civilians and journalists, is on trial as this story breaks.)
Via The Atlantic:
We don’t know a lot about how the government spies on us, but we know some things. We know the FBI has issued tens of thousands of ultra-secret National Security Letters to collect all sorts of data on people—we believe on millions of people—and has been abusing them to spy on cloud-computer users. We know it can collect a wide array of personal data from the Internet without a warrant. We also know that the FBI has been intercepting cell-phone data, all but voice content, for the past 20 years without a warrant, and can use the microphone on some powered-off cell phones as a room bug—presumably only with a warrant.
We know that the NSA has many domestic-surveillance and data-mining programs with codenames like Trailblazer, Stellar Wind, and Ragtime—deliberately using different codenames for similar programs to stymie oversight and conceal what’s really going on. We know that the NSA is building an enormous computer facility in Utah to store all this data, as well as faster computer networks to process it all. We know the U.S. Cyber Command employs 4,000 people.
We know that the DHS is also collecting a massive amount of data on people, and that local police departments are running “fusion centers” to collect and analyze this data, and covering up its failures. This is all part of the militarization of the police.
We know all of this not because the government is honest and forthcoming, but mostly through three backchannels—inadvertent hints or outright admissions by government officials in hearings and court cases, information gleaned from government documents received under FOIA, and government whistle-blowers.
The Obama administration may be remembered as the data-driven presidency: While Americans have decided to spend their time building the social Web by freely sharing their data online, the NSA and other agencies have been constructing a second Internet on the ashes of the TIA (Total Information Awareness) and ECHELON programs, one to real-time monitor all of the information that Americans don’t freely share. (Which isn’t much these days.) So now we have PRISM, a vast experiment in public data-mining (which some are suggesting originated with data-mining firm Palantir.)
While Facebook and the blogosphere go nuts covering the story, here’s some background information to show how we’ve gotten here.
– Investigative journalism outlet ProPublica collates a list of the top stories about US Government surveillance since 2005 at “The Best Stories on the Government’s Growing Surveillance.”
– Mother Jones provides a domestic surveillance timeline since 2001 at “The Domestic Surveillance Boom, From Bush to Obama.”
Even more usefully, ProPublica also provides a handy guide to exactly where and how the government can get your data, from your computer to your smart phone, here:
– “No Warrant, No Problem: How the Government Can Get Your Digital Data”
Confronted with the PRISM revelations, Obama’s response has been non-plussed. His official comment is “Nobody is listening to your telephone calls.” (The Guardian is currently live-updating .gov response to PRISMgate.) Senator Dianne Feinstein’s response was even more droll: “It’s called protecting America.” Others, however, have been less self-congratulatory—for instance, Senator Bernie Sanders (I-Vt.), who referred to the program as “Alarming and absolutely unacceptable” in an official statement.
But it goes beyond being simply “alarming and absolutely unacceptable” and into the sickening realization what we ourselves have helped to create is a voluntary surveillance state.
Consider Britain, parts of which are 100% saturated by surveillance cameras—an autocratic dream easy to accomplish on a tiny island, but far more expensive and difficult to execute in a country the size of the United States. What to do instead, then? Simple: Offer the means of surveillance as a free gift and make it so ubiquitous and narcissistically pleasing to use that your citizens will volunteer their information, whereabouts and personality profiles of their own free will. It’s called the smart phone, Facebook and Google-dominated Web, and it’s a marketer’s wet dream—and an NSA surveillance data-miner’s, too.
Why Does the Media Want to Hang Edward Snowden? (6/12/2013)

(This article was written by Ultraculture contributor Woody Evans.)
NSA surveillance whistleblower Edward Snowden—the man who leaked the doings of the PRISM program to the Guardian’s Glen Greenwald and Laura Poitras—currently has the eyes of the entire world on him. Snowden is an accomplished and self-made man; though he didn’t graduate high school, he rose high enough in the ranks of the United States security and intelligence machine to be able to “wiretap anyone from you or your accountant to a Federal judge to even the President” without a warrant. And he made a relatively large amount of money by keeping his fingers on those buttons.
Snowden has revealed that he (and how many others? hundreds? thousands?) had “authorities” to listen in to any of us. That word—”authorities”—has confused some commentators. By it Snowden does not mean the legal authority. He means ability. He means that he, as an individual operator in the system, had a piece of pwn-pie. He means that the NSA (and who else? DIA, CSS, INSCOM? Your local sheriff’s office if enough “pretty pleases” are offered?) owns you—in the hacker sense. (What, the Cult of the Dead Cow’s Mudge has been a director of research for DARPA since 2010 and you don’t reckon that the White Hats do in fact run the show?) Snowden has reminded us that the technocracy—whatever the individual aims, aspirations, or values of those who participate in it—has won. We are pwned.
One of the poorest comments on Snowden has come from David Brooks at the New York Times. He says that Snowden “betrayed the cause of open government.” He says that every new leak causes those in power to “close the circle of trust a little tighter” and further limit our debates about openness and privacy. He dismisses the fact that the “circle of trust” between the people and their government has long been broken. He just gives .gov a pass on the fact that our ability to debate is increasingly shut down.
Brooks attempts to draw conclusions about how Snowden as a new type of man (libertarian, distrustful, rabidly private) is tearing apart the common good of virtuous government. His conclusions are drawn from personal clues—Snowden is grumpy to his neighbors, Snowden votes libertarian. Snowden represents the “rise of people who are so individualistic in their outlook that they have no real understanding of how to knit others together and look after the common good,” Brooks says, despite Snowden’s own stated position: “If you realize that that’s the world you helped create and it’s gonna get worse with the next generation and the next generation who extend the capabilities of this sort of architecture of oppression, you realize that you might be willing to accept any risk and it doesn’t matter what the outcome is so long as the public gets to make their own decisions about how that’s applied.”
How does Snowden’s concern with the public’s ability to make its own decisions jibe with Brooks’ assertion that Snowden isn’t concerned with the common good?
Answer: It doesn’t.
Now, I must admit that I agree with part of Brooks’ sentiment, which I take to be something like wouldn’t it be nice if we could trust our governments, and shouldn’t we at least do our duties as if our governments are still worthy of trust? But that is only a Sentiment. Brooks is (intentionally?) ignoring the point of Snowden’s case and what it means for the rest of us. Brooks can’t get away with asking us to buy into a Sentiment in exchange for having us ignore that our governments are ignoring the Rule of Law. It seems to me that Brooks is either coming very close to lying to (as in misdirecting the attention of) his audience, or he needs a long vacation and a lot of vitamins and a lot of love making and a lot of sun bathing and a lot of book reading to jump start his brain. I don’t want to attack the man—but he’s attacking our intelligence if he expects us to buy such D-grade bullshit.
The point is that we have all been hacked.
The very way we think and talk about what’s just been revealed (oh, it’s just metadata… why worry if you don’t have anything to hide?) reveals the depth of the hack. We’ve been trained to accept that our data is not our own and that privacy is a privilege we can’t afford anymore. Your metadata, ladies and gentlemen, is still your metadata.
Brooks and others representing the consensus interests of the Homeland Security State sure are defending the NSA surveillance program and arguing for our continuing trust and acceptance that this hacking has been for justifiable reasons. But no continuity for “trust” has existed since 1963. Or after the Plumbers’ work in 1973. Or after Iran-Contra. Or the gutting of Chile and the execution of Allende. Or certainly after the New Century was christened with a lie that razed Iraq. What trust is left?
If we have been hacked, as individuals and as a society, if the police state is so total that physical resistance or even demonstration is not possible, and if we are indeed pwnd by technocrats, then what can we really expect the reaction of society, especially the younger generation, to be?
If Snowden’s revelations are treated as the mere “acting out” out of overly “individualistic” youth by those speaking for our fathers’ generation, then the anger of this generation may smolder into something much more hard-bitten and crystalline.
There will soon come day when those who err on the side of Lex is Rex realize in large numbers that legal code is Code, that the rules of exchange can be cryptocurrencied, and that the halls of power belong to the goth, witch, loser, seapunk and gamer every bit as much as they belong to the moneyed and cuff-linked and well-insured.
We have all been hacked. Why should they expect trust?
UK Intelligence Raids Guardian Offices, Destroys Snowden Info (8/20/2013)

New developments in the Snowden saga: After locking up Guardian journalist Glenn Greenwald’s partner David Miranda for nine hours, the British government have now raided the headquarters of the Guardian and destroyed forced the newspaper to destroy information relating to Edward Snowden’s NSA surveillance leaks and the Guardian’s stories about them—despite the fact that the information had already been disseminated elsewhere. It’s a brutal, banana republic-style intimidation tactic—and also a show of ignorance from the authorities about how diffuse information now is.
Via Reuters:
(Reuters) – The editor of the Guardian, a major outlet for revelations based on leaks from former U.S. intelligence contractor Edward Snowden, says the British government threatened legal action against the newspaper unless it either destroyed the classified documents or handed them back to British authorities.
In an article posted on the British newspaper’s website on Monday, Guardian editor Alan Rusbridger said that a month ago, after the newspaper had published several stories based on Snowden’s material, a British official advised him: “You’ve had your fun. Now we want the stuff back.”
After further talks with the government, Rusbridger said, two “security experts” from Government Communications Headquarters, the British equivalent of the ultra-secretive U.S. National Security Agency, visited the Guardian’s London offices.
In the building’s basement, Rusbridger wrote, government officials watched as computers which contained material provided by Snowden were physically pulverized. “We can call off the black helicopters,” Rusbridger says one of the officials joked.
There is a good, succinct summary of what’s happening at the Verge.
Guardian editor Alan Rusbridger discusses the raid here.
Windows 8 Contains Backdoor to Microsoft, NSA Surveillance, China (8/22/2013)

According to information leaked from the German government (the German Federal Office for Information Security), Microsoft operating system Windows 8 contains a backdoor, dubbed “Trusted Computing,” which allows Microsoft access and the ability to remotely control the computer of anybody using the OS. That same backdoor is very likely also open to not only NSA surveillance, but potentially the Chinese government, claims German-language magazine Die Zeit. (Original article, here, has to be translated from German by your browser. Unless, you know, you speak German.)
An English-language summary is below, via InvestmentWatch Blog:
Windows 8, the touch-screen enabled, super-duper, but sales-challenged Microsoft operating system is outright dangerous for data security. It allows Microsoft to control the computer remotely through a built-in backdoor. Keys to that backdoor are likely accessible to the NSA – and in an unintended ironic twist, perhaps even to the Chinese.
The backdoor is called “Trusted Computing,” developed and promoted by the Trusted Computing Group, founded a decade ago by the all-American tech companies AMD, Cisco, Hewlett-Packard, IBM, Intel, Microsoft, and Wave Systems. Its core element is a chip, the Trusted Platform Module (TPM), and an operating system designed for it, such as Windows 8. Trusted Computing Group has developed the specifications of how the chip and operating systems work together.
Its purpose is Digital Rights Management and computer security. The system decides what software had been legally obtained and would be allowed to run on the computer, and what software, such as illegal copies or viruses and Trojans, should be disabled. The whole process would be governed by Windows, and through remote access, by Microsoft.
Meanwhile in Germany, authorities just arrested a man that snuck onto Chancellor Merkel’s plane “clutching a bag full of marijuana and ecstasy pills, danced on a wing, sprayed extinguisher foam around the plane and pushed buttons in the cockpit before finally [being] arrested by police.” Seems like they need to keep security a little tighter over there. Now naked men are everywhere and the world knows about yet another plan by the intelligence/information-technology axis to keep tabs on the entire world.
NSA Chief is Spying on Everybody From a “Star Trek”-Themed War Room (9/16/2013)

Bizarre surveillance culture zen: NSA Chief Gen. Keith Alexander is spying on everybody from a command center built to look like the bridge of the Enterprise from Star Trek: The Next Generation, like a total psycho
General Keith Alexander, the chief of the NSA, apparently had a Star Trek-themed command center built in order to spy on the American population, in a psychotic collision of surveillance culture, pop culture and the general mental space of the country, all wrapped up in one bizarre news story.
Look, let’s get this straight: What Edward Snowden did fully, finally proves that there is another world. There is a world outside of the mundane drama played out for the average American citizen, a shadow world, the stuff of bad action movie plots and conspiracy theories. It’s like you’re in a movie and Wesley Snipes is explaining to you that vampires are real, and you better wise up to the shadow world.
Except that, post-Snowden, we know the shadow world is real. While it was once all too easy to dismiss ideas like “they’re spying on all of us” as tin-foil-hat fodder, now we know that the monster under the bed actually is real and the sky actually is falling. That’s huge, and it’s a reality we’re only beginning to even think about adjusting to. Too big, too scary and too real to cope with in the short-term.
But the shadow world is just like us. It’s a reflection, a dark mirror image. Consider the average American internet user—”checking up” on current and old friends on Facebook, attempting to get attention through social media, constantly expanding their electronic perception of the world, lurking Reddit, turning everything into a Star Trek or Star Wars or Breaking Bad reference.
How different is that from General Alexander sitting in his faux Picard chair while checking up on the whole country? It’s not different. It’s a matter of scale and of power but it’s… look. The guy in charge, the man behind the curtain, the guy peering through the Eye of Sauron at us all… he’s just like us. He’s just another Internet troll. And that’s the disturbing part: We’re staring at ourself. This NSA surveillance beast, this awful horrible thing that is spying on us all, is just a bigger version of us.
It has been previously reported that the mentality of NSA chief Gen. Keith Alexander is captured by his motto “Collect it All”. It’s a get-everything approach he pioneered first when aimed at an enemy population in the middle of a war zone in Iraq, one he has now imported onto US soil, aimed at the domestic population and everyone else.
But a perhaps even more disturbing and revealing vignette into the spy chief’s mind comes from a new Foreign Policy article describing what the journal calls his “all-out, barely-legal drive to build the ultimate spy machine”. The article describes how even his NSA peers see him as a “cowboy” willing to play fast and loose with legal limits in order to construct a system of ubiquitous surveillance. But the personality driving all of this – not just Alexander’s but much of Washington’s – is perhaps best captured by this one passage, highlighted by PBS’ News Hour in a post entitled: “NSA director modeled war room after Star Trek’s Enterprise”. The room was christened as part of the “Information Dominance Center”:
“When he was running the Army’s Intelligence and Security Command, Alexander brought many of his future allies down to Fort Belvoir for a tour of his base of operations, a facility known as the Information Dominance Center. It had been designed by a Hollywood set designer to mimic the bridge of the starship Enterprise from Star Trek, complete with chrome panels, computer stations, a huge TV monitor on the forward wall, and doors that made a ‘whoosh’ sound when they slid open and closed. Lawmakers and other important officials took turns sitting in a leather ‘captain’s chair’ in the center of the room and watched as Alexander, a lover of science-fiction movies, showed off his data tools on the big screen.
“‘Everybody wanted to sit in the chair at least once to pretend he was Jean-Luc Picard,’ says a retired officer in charge of VIP visits.”
Boing Boing has a video of the Star Trek-themed war room here, embedded below.
(Image via the Guardian.)
Greenwald Probes NSA Assassinations; McAfee Releases NSA Surveillance Blocking Device (9/30/2013)

The weekend’s new twists in the ongoing surreality of the NSA surveillance revelations: Greenwald investigates assassinations, countries race to provide data privacy, John McAfee launches “Decentral” project to thwart NSA surveillance
Things are getting even stranger, if possible, in the NSA surveillance saga: after having released Snowden’s documents, Guardian journalist Glenn Greenwald is now teaming up with The Nation‘s Jeremy Scahill to investigate the NSA’s connections to the United States’ covert assassination programs:
Glenn Greenwald, the Rio-based journalist who has written stories about U.S. surveillance programs based on documents leaked by former NSA contractor Edward Snowden, is now working with Jeremy Scahill, a contributor to The Nation magazine and the New York Times best-selling author of “Dirty Wars.”
“The connections between war and surveillance are clear. I don’t want to give too much away but Glenn and I are working on a project right now that has at its center how the National Security Agency plays a significant, central role on the U.S. assassination program,” said Scahill, speaking to moviegoers in Rio de Janeiro, where the documentary based on his book made its Latin American debut at the Rio Film Festival.
The recent NSA surveillance revelations have sparked competition to see who can offer data privacy: countries like Germany are competing to see who can be the “Cayman islands” of secure data.
Fueled by the controversy, countries are seeking to use data-privacy laws as a competitive advantage—a way to boost domestic companies that long have sought an edge over Google, Microsoft Corp. MSFT +1.50% and other U.S. tech giants.
“Countries are competing to be the Cayman Islands of data privacy,” says Daniel Castro, a senior analyst at the Information Technology and Innovation Foundation, a nonpartisan Washington, D.C., think tank that receives funding from the tech industry.
While establishing these islands of privacy might make for good marketing, the initiatives face hurdles. Laws demanding that data be stored in-country can give domestic Internet-service providers a boost but also could raise their customers’ costs.
And best of all in NSA surveillance related news, infamous software mogul and bath salts aficionado John McAfee, not one to be left out of controversy, has announced plans to launch “Decentral,” a $100, pocket-sized device that he claims will block NSA surveillance.
Via the San Jose Mercury News:
John McAfee lived up to his reputation Saturday as tech’s most popular wild child, electrifying an audience with new details of his plan to thwart the NSA’s surveillance of ordinary Americans with an inexpensive, pocket-size gadget.
Dubbed “Decentral,” the as-yet-unbuilt device will cost less than $100, McAfee promised the enthusiastic crowd of about 300 engineers, musicians and artists at the San Jose McEnery Convention Center.
“There will be no way (for the government) to tell who you are or where you are,” he said in an onstage interview with moderator Dan Holden at the inaugural C2SV Technology Conference + Music Festival.
If that wasn’t enough dirty NSA surveillance news, new reports have revealed that the agency spied on US senators during the Vietnam era—and that the NSA additionally mines US citizens’ Facebook accounts to develop profiles of their personalities and social networks. Surprise?
(Image via.)
The NSA Lied: NSA Surveillance Didn’t Stop 54 Terror Plots (10/15/2013)

General Alexander lied about how NSA surveillance is being used, and he’s been caught in public
The NSA recently attempted to justify its mass surveillance programs by claiming that its secret taps had foiled 54 terrorist plots.
Except that’s not true. And General Alexander (the same psycho that built a surveillance “command center” to spy on Americans, and designed it to look like the bridge of the Enterprise from Star Trek) has been caught out lying about the whole thing. And Senator Patrick Leahy (D-Vermont), current chairman of the Senate Judiciary Committee, is none too pleased.
Via the State Weekly:
The head of the National Security Agency (NSA) admitted before a congressional committee this week that he lied back in June when he claimed the agency’s phone surveillance program had thwarted 54 terrorist “plots or events.”
NSA Director Keith Alexander gave out the erroneous number while the Obama administration was defending its domestic spying operations exposed by whistleblower Edward Snowden. He said surveillance data collected that led to 53 of those 54 plots had provided the initial tips to “unravel the threat stream.
But Senator Patrick Leahy (D-Vermont), chairman of the Senate Judiciary Committee, said on Wednesday during a hearing on the continued oversight of the Foreign Intelligence Surveillance Act that the administration was pushing incomplete or inaccurate statements about the bulk collection of phone records from communications providers.
Meanwhile, in response to NSA surveillance, Germany is closing its doors and planning on constructing a Germany-only communications network to block further NSA surveillance.
Senator Dianne Feinstein Wants NSA Surveillance Made Official, Permanent (10/28/2013)

California Senator Dianne Feinstein is proposing a bill that will make the NSA’s PRISM program official and legal
Senator Dianne Feinstein (D-Ca.) is planning a bill to codify NSA surveillance into law, in the latest news in Draconian Subreptilian Fuckery. The legislation would make NSA spying official and legal, and the explicit ability to gather metadata on all phone calls within the United States. Feinstein is positioning the bill to preserve the NSA’s activities while adding token gestures to civil liberties—but that isn’t stopping both the left and the right, and notably Senator Patrick Leahy (D-Vt.) from taking her to task on her proposed bill.
Via SFGate:
California Sen. Dianne Feinstein has set up a clash with another powerful senior Democrat and drawn criticism from civil libertarians on the left and right for her defense of a national security program that collects Americans’ telephone records.
The role is a familiar one for Feinstein, whose pro-law enforcement outlook has persisted from her days on a women’s parole board and her tenure as San Francisco mayor. Now it’s in full evidence in her leadership of the Senate Select Committee on Intelligence, which oversees the U.S. spy apparatus.
“I do not want to leave the United States in a position where we are open to another major attack because we can’t ferret out who terrorists might be calling in this country to put it together,” Feinstein said in an interview.
So Senator Feinstein wants to “ferret out who terrorists might be calling”… but who, exactly, is a terrorist? Luckily, Activist Post has rounded up all 72 ways to get classed as a terrorist in America, including those who talk about “individual liberties” and “those who want to make the world a better place” here.
Meanwhile, more information is surfacing on the NSA’s connection to Israel—and how the NSA has been outright handing over US data to the Israelis (!?).
Below, Glenn Greenwald on Democracy Now! takes Dianne Feinstein to task for outright lying about how the NSA surveillance program is used. Greenwald just revealed that the US is eavesdropping on Spain (right after the US has come under extreme fire for spying on German Chancellor Angela Merkel, as well as massively spying on Mexico and France), and that US embassies are used as wiretapping hubs in foreign countries.
You can, by the way, tell Sen. Feinstein to go fuck herself here.
How to Game the NSA’s CO-TRAVELLER Program (12/17/2013)

(This post by Ultraculture contributor Woody Evans.)
The Electronic Frontier Foundation wrote about the NSA’s CO-TRAVELER program in a post last week:
“… CO-TRAVELER, is designed to track who meets with whom and covers everyone who carries a cell phone, all around the world. With neither public debate nor court authorization, CO-TRAVELER collects billions of records daily of cell phone user location information. It maps the relationships of cell phone users across global mobile network cables, gathering data about who you are physically with and how often your movements intersect with other cell phone users. The program even tracks when your phone is turned on or off.”
Records from CO-TRAVELER go into a database of locations and relationships called FASCIA. Data on who you meet, when and where you meet, and how long you are with those you meet is then available for government agencies to search. Would the patterns found in FASCIA about you and your relationships be used as circumstantial evidence for… whatever they would want to pin on you? The existence of this program also creates a real-world, analog chilling effect—you’ll think twice about going to that vegan diner, for instance, since you know the straight-edge punks there have a soft-spot for the Occupy movement. You might not want to be affiliated with that scene now, even though all you really want is some spicy seitan fajitas.
Consider the following FASCIA-affronting thought experiment.
You’re headed to your favorite coffee shop on Precinct Line Road, and you don’t want to be accidentally “affiliated” with the strangers grabbing a cup of coffee while you’re there. You’re planning to meet your Alcoholics Anonymous sponsor, and it occurs to you that she meets with lots of drunks and junkies. It would be a shame for you to be noted by the Feds as being one degree of separation away from a former South Fort Worth drug dealer. Also, what’s with all the Sikhs in Euless these days? You don’t know, and you don’t even know the difference between a Sikh and a Muslim, but you reckon it would be better if you weren’t “affiliated” in FASCIA with any coffee drinkin’ and donut lovin’ Sikh grandads that might wander into the place. And then there are the secessionist white boys who come to town when the moon is full, and they like donuts too, right? So, you decide, it’s probably better if you’re not in FASCIA.
In fact, the owner of the coffee shop doesn’t want the “all-welcome and have donuts anonymously” business model of his place make him some kind of liability in the eyes of the Feds. And neither would the CEO of Target, or the Wendy’s just around the corner, or the Hmong family that run the dry cleaner’s by the tabernacle, for that matter. Bad for business all around.
So all the regular customers to this little shopping plaza start having conversations with the managers and landlords, and you all come to the following arrangement: Upon entering the block, you may place your phone in a locker in the parking lot. Take a key. It will be one tiny locker of thousands. When you’re done getting coffee or buying your dishwashing liquid or whatever, you pick up your phone from the locker.
The locker has put your identity and location into a much larger pool. Now FASCIA won’t only note the correlations between you and the other folks in your favorite coffee shop, but the correlations will map “meetings” between the thousands who were at all and any of the businesses on that block during that hour. The presumed correlations and affiliations will therefore mean less and be full of more noise and false positives. CO-TRAVELER then becomes a victim of its own success; FASCIA becomes full of connections between, well, everybody. And if everybody is connected to everyone else in town, can FASCIA say anything meaningful about your private associations with your AA sponsor? Or a friendly chat with a Sikh at the liquor store? Or your multiple meetings with your preacher’s ex-wife?
It’s just a thought—and maybe the “locker” system is just a metaphor or starting point for better systems for something like a “citizen trade craft” or “privacy trade craft” (which is now required to protect our rights). Too much information in a system increases the likelihood that any one apparent signal is actually noise. The system becomes useless, or nearly so.
And then we can get back to meeting each other (and reaching out to dialogue with “the other”) without fear. Right?
Edward Snowden Offers to Help Brazil Uncover NSA Surveillance in Exchange for Political Asylum (12/17/2013)

Edward Snowden just offered to help Brazil uncover NSA surveillance in exchange for political asylum. Read the full text of his letter below
Edward Snowden (who’s currently still homeless) just wrote an open letter to Brazil, offering to help the country investigate how much the NSA has compromised their security in exchange for asylum. (Snowden’s leaked documents revealed that Brazil—where journalist Glenn Greenwald and his partner David Miranda live—is a major target for NSA surveillance.)
In the letter, Snowden dismisses claims that NSA surveillance is about safety or circumventing terrorism, stating instead that “These programs were never about terrorism: they’re about economic spying, social control, and diplomatic manipulation. They’re about power.”
CNN responded to the letter by Tweeting, and then deleting, a message that Snowden was offering to spy on the US:

To which Glenn Greenwald retorted:
Reproduced below is the entirety of Snowden’s letter to the emerging superpower, which bears a Creative Commons Attribution-Share Alike 3.0 License and is taken from Greenwald’s partner David Miranda’s Facebook.
Snowden says:
Six months ago, I stepped out from the shadows of the United States Government’s National Security Agency to stand in front of a journalist’s camera. I shared with the world evidence proving some governments are building a world-wide surveillance system to secretly track how we live, who we talk to, and what we say. I went in front of that camera with open eyes, knowing that the decision would cost me family and my home, and would risk my life. I was motivated by a belief that the citizens of the world deserve to understand the system in which they live.
My greatest fear was that no one would listen to my warning. Never have I been so glad to have been so wrong. The reaction in certain countries has been particularly inspiring to me, and Brazil is certainly one of those.
At the NSA, I witnessed with growing alarm the surveillance of whole populations without any suspicion of wrongdoing, and it threatens to become the greatest human rights challenge of our time. The NSA and other spying agencies tell us that for our own “safety”—for Dilma’s “safety,” for Petrobras’ “safety”—they have revoked our right to privacy and broken into our lives. And they did it without asking the public in any country, even their own.
Today, if you carry a cell phone in Sao Paolo, the NSA can and does keep track of your location: they do this 5 billion times a day to people around the world. When someone in Florianopolis visits a website, the NSA keeps a record of when it happened and what you did there. If a mother in Porto Alegre calls her son to wish him luck on his university exam, NSA can keep that call log for five years or more. They even keep track of who is having an affair or looking at pornography, in case they need to damage their target’s reputation.
American Senators tell us that Brazil should not worry, because this is not “surveillance,” it’s “data collection.” They say it is done to keep you safe. They’re wrong. There is a huge difference between legal programs, legitimate spying, legitimate law enforcement — where individuals are targeted based on a reasonable, individualized suspicion — and these programs of dragnet mass surveillance that put entire populations under an all-seeing eye and save copies forever. These programs were never about terrorism: they’re about economic spying, social control, and diplomatic manipulation. They’re about power.
Many Brazilian senators agree, and have asked for my assistance with their investigations of suspected crimes against Brazilian citizens. I have expressed my willingness to assist wherever appropriate and lawful, but unfortunately the United States government has worked very hard to limit my ability to do so — going so far as to force down the Presidential Plane of Evo Morales to prevent me from traveling to Latin America! Until a country grants permanent political asylum, the US government will continue to interfere with my ability to speak.
“These programs were never about terrorism: they’re about economic spying, social control, and diplomatic manipulation. They’re about power.”
Six months ago, I revealed that the NSA wanted to listen to the whole world. Now, the whole world is listening back, and speaking out, too. And the NSA doesn’t like what it’s hearing. The culture of indiscriminate worldwide surveillance, exposed to public debates and real investigations on every continent, is collapsing. Only three weeks ago, Brazil led the United Nations Human Rights Committee to recognize for the first time in history that privacy does not stop where the digital network starts, and that the mass surveillance of innocents is a violation of human rights.
The tide has turned, and we can finally see a future where we can enjoy security without sacrificing our privacy. Our rights cannot be limited by a secret organization, and American officials should never decide the freedoms of Brazilian citizens. Even the defenders of mass surveillance, those who may not be persuaded that our surveillance technologies have dangerously outpaced democratic controls, now agree that in democracies, surveillance of the public must be debated by the public.
My act of conscience began with a statement: “I don’t want to live in a world where everything that I say, everything I do, everyone I talk to, every expression of creativity or love or friendship is recorded. That’s not something I’m willing to support, it’s not something I’m willing to build, and it’s not something I’m willing to live under.”
Days later, I was told my government had made me stateless and wanted to imprison me. The price for my speech was my passport, but I would pay it again: I will not be the one to ignore criminality for the sake of political comfort. I would rather be without a state than without a voice.
If Brazil hears only one thing from me, let it be this: when all of us band together against injustices and in defense of privacy and basic human rights, we can defend ourselves from even the most powerful systems.
Edward Snowden ‘Already Won’, But the NSA Surveillance Nightmare Continues (12/24/2013)

Edward Snowden emerged from hiding this morning to announce that he had “already won” the fight against NSA surveillance. Via the Washington Post:
“For me, in terms of personal satisfaction, the mission’s already accomplished,” he said. “I already won. As soon as the journalists were able to work, everything that I had been trying to do was validated. Because, remember, I didn’t want to change society. I wanted to give society a chance to determine if it should change itself.”
“All I wanted was for the public to be able to have a say in how they are governed,” he said. “That is a milestone we left a long time ago. Right now, all we are looking at are stretch goals.”
But that’s just the tip of the iceberg in terms of the last two weeks’ worth of total and utter political anarchy that have continued to destabilize geopolitics in the wake of Snowden’s revelations.
Last Monday, U.S. District Judge Richard J. Leon ruled that NSA surveillance of phone records is almost certainly unconstitutional, stating in his 68-page ruling that “I cannot imagine a more ‘indiscriminate’ and ‘arbitrary invasion’ than this systematic and high tech collection and retention of personal data on virtually every single citizen for purposes of querying and analyzing it without prior judicial approval. Surely, such a program infringes on ‘that degree of privacy’ that the founders enshrined in the Fourth Amendment.” Leon’s statement marked the first time ever that a federal judge has given an opinion in open court on the collection of lawfulness in a non-criminal case. The Justice Department is reviewing Leon’s decision, and maintaining that the NSA surveillance program is constitutional. Though it is unlikely the ruling will actually have any legal impact, Snowden has been publicly jubilant over Leon’s decision. Richard J. Leon was appointed by George W. Bush; while Larry Klayman, the legal activist who filed the initial suit, is a staunch right-winger—CNN cut him off while on-mic in a rather shocking display of Fox News-style censorship. Klayman has since complained of harassment by the US authorities.
Senator Dianne Feinstein, a staunch ally of the NSA, responded to the ruling with the rather weasel-y statement that the NSA surveillance program is “important” but not “indispensable” for preventing terrorism, suggesting she may simply be waiting to cover herself and switch to whatever side of the NSA surveillance debate wins in the public and political discourse, and stated she would be waiting for a Supreme Court decision on the program’s constitutionality. Benjamin Wittes of Washington think-tank the Brookings Institution highly doubts that the Supreme Court would be bold enough to shut down the program, however.
At the opposite end of the political spectrum, Senators Ron Wyden, Mark Udall and Martin Heinrich, all on the Senate Intelligence Committee and privy to classified NSA briefings, have issued a “friend of the court” brief that NSA surveillance not only has never stopped a single terrorist attack, but that it actively hinders the prevention of terrorism, stating that “as members of the committee charged with overseeing the National Security Agency’s surveillance, Amici [i.e. the three senators as well as allied security experts] have reviewed this surveillance extensively and have seen no evidence that the bulk collection of Americans’ phone records has provided any intelligence of value that could not have been gathered through less intrusive means” and that the public “should view the government’s claims regarding the effectiveness of its surveillance programs with searching skepticism and demand evidence rather than assurances before accepting them.” (When asked by Reuters on December 20 about whether the NSA’s secret programs had ever stopped a terrorist attack, Obama tellingly dodged the question.)
Senators Ryden, Udall and Heinrich are not alone in their summation of the NSA surveillance secret programs’ effectiveness. Agreeing with them are Richard A. Clarke, the former National Coordinator for Security, Infrastructure Protection and Counterterrorism, who served as counterterrorism expert under both Bushes and Bill Clinton; 9/11 commission co-chairs Thomas H. Kean and Lee H. Hamilton; Bill Clinton and even the President’s specially appointed Review Group on Intelligence and Communication Technologies, who found that NSA surveillance was practically useless for counterterrorism—and recommended over 40 changes be made to the NSA. Bill Binney, former senior technical director at NSA before resigning shortly after 9/11, who created the NSA surveillance systems in the first place, has stated that the US is “now in a police state.”
The USA Freedom Act, a bill written by Rep. Jim Sensenbrenner (R-Wis.)—the original author of the fricking PATRIOT Act—specifically to rein in NSA power and end the spying programs, already has 107 co-sponsors in the house; while Sen. Patrick Leahy (D-Vt.)’s version for the Senate has 18. Leahy memorably stated in October that “we get more in the newspapers than in classified briefings.”
Glenn Greenwald has publicly stated that the goal of the NSA is to eliminate privacy worldwide, stating that “I think western governments have inculcated people to accept that privacy does not really have much value” and that this was “to get populations accustomed to violations of their privacy.” One NSA official, outraged at the press uncovering the agency’s programs, has actually publicly stated that “I have some reforms for the First Amendment.”
Foreign uproar has continued. Chancellor Merkel, already outraged over the NSA tapping her phone (and now leading a rejection of US drones), has stated through a spokesman that US contracting companies should be banned from handling the German military’s data, which certainly makes sense. In an angry phone exchange with Obama, Merkel compared the NSA’s programs to the Stasi, the communist secret police in the East Germany of her youth. Information has surfaced that the NSA was not only spying on Merkel but targets in over sixty nations, including an Israeli prime minister and officials throughout the European Union. Also in Germany, Snowden ally, former WikiLeaks representative and Tor developer Jacob Applebaum, currently living in Berlin, has claimed he is under aggressive surveillance by the United States even while on German soil. Not all in Europe are so reticent to join the NSA surveillance free-for-all, however: Sweden has just been granted access to the NSA’s XKeyscore program, and which allows for the collection of online behavior worldwide.
The heads of tech companies Google, Apple, Netflix, Yahoo and Twitter all took a private meeting with Obama on December 17, pushing on him to drop online spying after stating publicly that “The balance in many countries has tipped too far in favor of the state and away from the rights of the individual—rights that are enshrined in our Constitution”—though the same companies directly cooperated with the NSA surveillance programs! (!) (!) (!) (It’s been noted that Edward Snowden didn’t show up on any of Google’s top searches for 2013—potentially on purpose.)
Meanwhile, job applications to the NSA are down by over 1/3.
The NSA is Building a Quantum Supercomputer (1/3/2014)

The NSA’s proposed quantum supercomputer—and a treasure trove of info on what’s been happening with NSA surveillance
According to new Snowden documents, the NSA is building a quantum supercomputer (quantum computers, which are still largely on the drawing board, will harnass vast computing power far beyond anything currently known to the civilian market) in order to crack encryption. At which point, might as well forget about Tor and PGP…?
[Addendum: However, getting this working properly may be decades off, so there’s no need to think encryption tools like Tor won’t work at present—the NSA has repeatedly attempted to compromise Tor, but they haven’t yet been able to, according to the Guardian. Still—use at your own risk.]
Via Phys.org:
The US National Security Agency is making strides toward building a “quantum computer” that could break nearly any kind of encryption, The Washington Post reported Thursday.
The Post said leaked documents from fugitive ex-NSA contractor Edward Snowden indicate the computer would allow the secret intelligence agency to break encryption used to protect banking, medical, business and government records around the world.
Quantum computing has been a goal among commercial firms such as IBM because it could harness the power of atoms and molecules, vastly increasing speed and security of computers and other devices.
But experts cited by the newspaper said it was unlikely that the NSA would be close to creating such a machine without the scientific community being aware of it.
Here’s a roundup of more NSA surveillance news from the last two weeks, which is flying by too quickly to keep up with. Because of the memetic nature of news sharing, it’s also very hard to connect dots between news stories reported at various outlets all over the web—here’s what I’ve collated on NSA surveillance:
Predictably but awfully, a federal judge has ruled that NSA surveillance of phones is constitutional (Reuters)
The NSA has total and absolute access to the Apple iPhone (Forbes)
Meanwhile, a Stanford researcher has revealed that despite the fact that the NSA and Obama like to claim phone spying is OK because they’re only collecting metadata, individuals can be easily identified by said metadata… even with a simple Google search (TechCrunch)
UN human rights chief Navi Pillay has stated privacy is as important as human rights and compared the uproar against the NSA surveillance to the anger that defeated South African apartheid (The Guardian)
The NSA’s elite “TAO” hacking unit infiltrates computers around the world, intercepts shipments of laptops to implant back doors (Der Spiegel)
Said hackers can get into your WiFi from up to eight miles away among many other bizarre technological exploits (The Verge). This info was delivered by Jacob Applebaum at his absolutely essential address at 30c3, linked below.
The US is now the world’s number one buyer of malware (Reuters)
The NSA has a 50-page catalog of tools for creating and exploiting backdoors (also written up by Jacob Applebaum at Der Spiegel). There’s a mind-boggling breakdown of said tools at ArsTechnica.
American IT firms have lost billions thanks to Snowden’s revelations (The Independent)
Reddit is still full of anti-Snowden shills and bots, as this graphic demonstrates (Imgur)
In case you need more catching up, here’s a great rundown of the 10 most important NSA surveillance leaks in 2013. (Daily Dot)
Most of the above revelations come from security researcher/Tor developer/Wikileaks cohort Jacob Applebaum’s address at the 30th Chaos Communications Congress in Hamburg. If you want one long video or movie this weekend, make it this one. Stick with the whole thing—it’s fascinating.
Julian Assange Reacts to Obama’s NSA Surveillance Speech; Slowly Becoming Gandalf (1/17/2014)

Below, Julian Assange reacts to Obama’s speech on curtailing NSA surveillance power this morning, calling Obama on a multitude of deceptions. Also, what’s up with the Gandalf look?
Ever Visit WikiLeaks.org? UK Intelligence Was Watching You (2/18/14)

US and UK intelligence went after WikiLeaks and visitors to WikiLeaks.org; considered going after Anonymous and even the Pirate Bay
This morning, Glenn Greenwald’s new Intercept blog revealed some new key info from Edward Snowden’s files. And while this isn’t exactly going to surprise, well, anybody on Earth, the NSA and GCHQ were spying on WikiLeaks. But more specifically:
• The NSA was directly interested in going after “the human network that supports WikiLeaks,” in an operation dubbed ANTICRISIS GIRL.
• GCHQ (the British intelligence agency that conducts NSA-style surveillance in the UK) collected the IP addresses of everybody who visited WikiLeaks.org, as well as the Google search terms used to get there.
• The Obama administration pushed to have foreign allies press criminal charges against Julian Assange, as retaliation for publishing the Afghanistan war logs. (Hmm….)
• Documents reveal a discussion among NSA officials over whether to dub WikiLeaks a “malicious foreign actor,” which would have allowed extensive NSA surveillance, even of US citizens involved with WikiLeaks.
• The NSA was also considering using its full surveillance system to come down on the Pirate Bay and Anonymous.
The full, excellent Glenn Greenwald article, which contains extensive information on all of the above, is linked below.
Via Glenn Greenwald’s Intercept:
Top-secret documents from the National Security Agency and its British counterpart reveal for the first time how the governments of the United States and the United Kingdom targeted WikiLeaks and other activist groups with tactics ranging from covert surveillance to prosecution.
The efforts – detailed in documents provided previously by NSA whistleblower Edward Snowden – included a broad campaign of international pressure aimed not only at WikiLeaks founder Julian Assange, but at what the U.S. government calls “the human network that supports WikiLeaks.” The documents also contain internal discussions about targeting the file-sharing site Pirate Bay and hacktivist collectives such as Anonymous.
One classified document from Government Communications Headquarters, Britain’s top spy agency, shows that GCHQ used its surveillance system to secretly monitor visitors to a WikiLeaks site. By exploiting its ability to tap into the fiber-optic cables that make up the backbone of the Internet, the agency confided to allies in 2012, it was able to collect the IP addresses of visitors in real time, as well as the search terms that visitors used to reach the site from search engines like Google.
How long will America and Britain allow this to continue?
Trolls Are Probably Working for Intelligence Agencies: Glenn Greenwald (2/25/14)

Glenn Greenwald reveals absolutely terrifying GCHQ presentation detailing how to disrupt online communities and discredit activists
God bless Glenn Greenwald.
Over at The Intercept, Greenwald has revealed more NSA surveillance documents: This time, about—oh fuck, really? Yes, it’s all right here—how intelligence agencies manipulate and disrupt online discourse. Among the revelations are:
– “Honey traps” (aka compromising people with sexual set-ups—a la Julian Assange)
– Virus attacks
– Anonymous has been targeted with DDoS attacks (the same ones Anonymous uses)
– YouTube and Blogger are closely monitored
More specifically, and more worryingly, Greenwald reports on the GCHQ (the British equivalent of the NSA) once-secret unit JTRIG (Joint Threat Research Intelligence Group)’s tactics for breaking online discourse. Greenwald identifies the JTRIG’s goals thusly:
Among the core self-identified purposes of JTRIG are two tactics: (1) to inject all sorts of false material onto the internet in order to destroy the reputation of its targets; and (2) to use social sciences and other techniques to manipulate online discourse and activism to generate outcomes it considers desirable. To see how extremist these programs are, just consider the tactics they boast of using to achieve those ends: “false flag operations” (posting material to the internet and falsely attributing it to someone else), fake victim blog posts (pretending to be a victim of the individual whose reputation they want to destroy), and posting “negative information” on various forums
Some of the further techniques that Greenwald reveals intelligence agencies use to destroy and discredit the reputations of the people they deem threats are:
– Changing photos on social networking sites
– Writing fake blog posts claiming to be victimized by the person
– Sending e-mails and texts to their colleagues, neighbors, friends.
Similar techniques—like posting negative info on social networks, leaking confidential info, and destroying business agreements—are used against companies. The JTRIG also explicitly lists its four commandments or “4 D’s” as “Deny / Disrupt / Degrade / Deceive.” It’s also important to note that these techniques, which are earmarked to be used against “hacktivists,” are to be used in lieu of traditional law-enforcement techniques—against people who have never been charged or convicted of any crime—citizens targeted merely for their political leanings.
RELATED: 10 Ways to Protect Yourself From NLP Mind Control
The full documents, all available in Greenwald’s article, detail “Magic Techniques & Experiment” (seriously, you can’t make this sh*t up) for manipulating online discourse, destroying reputations and busting up online groups. The techniques read very much like the real-world tactics used against protest groups in the United States’ Operation COINTELPRO, which worked to diffuse the Black Panthers, environmentalist groups and other civic protest groups. That these documents make repeated reference to “Magic” is beyond me. They also incorporate a broad range of techniques from social psychology and Neuro-Linguistic Programming, such as mirroring.
Reddit Shills Come Out in Full Force to Sink Glenn Greenwald (2/26/14)

Reddit goes hog-wild trying to censor Glenn Greenwald’s revelations that intelligence agencies are crafting and disrupting online discourse
Yesterday, Glenn Greenwald released what may be the most explosive document in the Snowden files—a GCHQ slideshow depicting tactics for destabilizing and destroying online discourse using trolling and related strategies, including bizarre slides urging GCHQ employees to become “Cyber Magicians” and employ psychology and Neuro-Linguistic Programming techniques to break up online dissent.
Not surprisingly, the story was immediately killed at Reddit—and killed over and over again by the mods, until it finally slipped through the, ahem, “shill-net” to finally see the light of day. Reddit, which purports to follow a democratic model of information-sharing, where individual users can up-vote or down-vote specific stories, with the ones that are most up-voted receiving the most attention, has been known to be non-neutral ground since, I dunno… oh, right. Since the government came down hard on the guy who created it and he hung himself for raiding files from JSTOR, rather than face 35 years in prison. Major tell right there. Nudge nudge wink wink.
ZeroHedge covers the regular killing of the Greenwald GCHQ story at /r/news and /r/worldnews, with screenshots:
The moderators at the giant r/news reddit (with over 2 million readers) repeatedly killed the Greenwald/Snowden story on government manipulation and disruption of the Internet … widely acknowledged to be one of the most important stories ever leaked by Snowden.
Similarly, the moderators at the even bigger r/worldnews reddit (over 5 million readers) repeatedly deleted the story, so that each new post had to start over at zero.
The story did, however, finally make it into the /r/worldnews and /r/news ecosystem, and finally shot to the very top of the /r/worldnews subreddit (my own article on the NSA’s Mexico installation, from VICE News, was hanging out in the #5 position). Once it made it to the front page, however, the “downvote brigade,” as Redditors (possibly shills or bots) who show up in droves to push controversial stories out of the limelight are sometimes called, quickly pushed it down.
Once Greenwald’s story made it to the top of /r/worldnews, however, commentors immediately started asking questions about why it had been suppressed.
Via a Redditor whose account has apparently been deleted, who also outs some of the shady tactics that have long been used to discredit the /r/conspiracy board:
Why is this story being removed from all the popular subs over and over by mods?
Message the admins[1] about the censorship of this article by /r/news[2] and /r/worldnews[3] mods. They have never seemed to care about this in the past but if enough users message them it will hopefully at least provoke a response of some kind. Something needs to be done about this or this site needs to be abandoned as a platform for legitimate political discourse.
Important Update: So, it turns out that the /r/news[4] mod /u/BipolarBear0[5] who has been deleting all the instances of this story has previously been caught running a voting brigade to get anti-Semitic content upvoted on /r/conspiracy to discredit the sub[6] . A fact which he admitted to me in another thread[7] just a few minutes ago (he claims he was doing an “experiment”…) . This guy needs to be banned from the site.
Over at /r/psychonaut, which is one of the few places on Reddit to get good information—outside of, ironically, the /r/conspiracy board, another Redditor breaks down a full list of the times the Greenwald article was pulled:
Via Redditor Alethios:
Compilation of all the times this story has been removed from Reddit:
https://pay.reddit.com/r/longtail/comments/1yw2nf/17977348_snowden_files_how_covert_agents/[1]
https://pay.reddit.com/r/longtail/comments/1ywl9l/60710537_leaked_gchq_document_admits_spy_agency/[2]
https://pay.reddit.com/r/longtail/comments/1ywkxv/3481820605_greenwald_how_covert_agents_infiltrate/[3]
https://pay.reddit.com/r/undelete/comments/1yw27h/9952966_the_conspiracy_theory_is_true_agents/[4]
https://pay.reddit.com/r/worldnews/comments/1yue1i/greenwald_how_covert_agents_infiltrate_the/[5]
https://pay.reddit.com/r/longtail/comments/1yvd0k/94717963_greenwald_article_how_covert_agents/[6]
https://pay.reddit.com/r/news/comments/1yux9i/greenwald_how_covert_agents_infiltrate_the/[7]
https://pay.reddit.com/r/news/comments/1yuut8/how_covert_agents_infiltrate_the_internet_to/[8]
https://pay.reddit.com/r/news/comments/1yxb1r/snowden_training_guide_for_gchq_nsa_agents/[9]
https://pay.reddit.com/r/news/comments/1yxkbv/new_nsa_leak_gchqs_dirtytricking_psyops_groups/[10]
https://pay.reddit.com/r/news/comments/1yxkw0/western_spy_agencies_build_cyber_magicians_to/[11]
https://pay.reddit.com/r/news/comments/1yx8zk/how_covert_agents_infiltrate_the_internet_to/[12]
Downvote brigade gearing up as the story rapidly slips down the rankings on the front page.
Confirms for me the causes behind the apparent slow decline of any genuine news on the front page (Celebrity Deaths, Olympic News and Natural Events aside). When was the last time we heard anything about Monsanto continuing to shit on people from a great height? When did we last hear about anything real really?
I suppose it’s pretty common knowledge by now that the mass media are little better than mouthpieces for the establishment. Now, we’re forced to conclude that the conversation online (particularly in the larger subreddits and websites) is just as badly manipulated.
Same tactics as those used against the counter-culture in the 60s, just on a wider scale.
If there was any remaining shred of naïveté left that intelligence and corporate authorities aren’t crafting and molding online discourse, I would hope you have now been disabused of it. I will note that the collective power of online interest in non-bullshit, however, tends to overwhelm shill and bot attacks, and this stuff always does make it into the public awareness despite all best efforts to the contrary. But how much of a toll does the great Distraction Machine—whether directly imposed by authorities, or by our own noisy online chatter and vapid sharing—take on the public mind? Quite a bit, I’d say, gauging by the number of freedoms we’ve lost in the last decade.
Keep sharing and upvoting the things that matter.
NSA Planning Malware Assault on the Internet (3/12/14)

New documents released revealing plans for a wide-scale NSA assault on computers worldwide
Ryan Gallagher and Glenn Greenwald at The Intercept just revealed that the NSA has plans to infect millions of computers worldwide with malware implants through an automated process—often by masquerading as a fake Facebook server. Earlier reports suggest that between 85,000 and 100,000 implants have already been deployed.
Some key malware programs are:
• UNITEDRAKE, which can allow complete control of a computer;
• CAPTIVATEDAUDIENCE, which can take control of a microphone to record conversations happening near the computer;
• HAMMERCHANT and HAMMERSTEIN, which can help in exploitation attacks at data sent through a VPN.
• QUANTUMSKY, which can block access to specific websites;
• QUANTUMCOPPER, which can corrupt downloads;
Along with many others. Worryingly, these seem able to circumvent many of the publicly available privacy and encryption solutions—the malware, according to the report, can circumvent encryption software, because it’s already in the computer before the encryption is employed.
Top-secret documents reveal that the National Security Agency is dramatically expanding its ability to covertly hack into computers on a mass scale by using automated systems that reduce the level of human oversight in the process.
The classified files – provided previously by NSA whistleblower Edward Snowden – contain new details about groundbreaking surveillance technology the agency has developed to infect potentially millions of computers worldwide with malware “implants.” The clandestine initiative enables the NSA to break into targeted computers and to siphon out data from foreign Internet and phone networks.
The covert infrastructure that supports the hacking efforts operates from the agency’s headquarters in Fort Meade, Maryland, and from eavesdropping bases in the United Kingdom and Japan. GCHQ, the British intelligence agency, appears to have played an integral role in helping to develop the implants tactic.
Meanwhile, Congress is losing their shit over just-revealed CIA spying on its members—it seems the outrage of foreign leaders who were bugged (like German Chancellor Angela Merkel) has come home.
The NSA is Stealing Your Face (6/2/2014)

New Snowden leaks reveal that the NSA is scraping 55,000 facial images a day from e-mails, texts, social media, Skype and more—and there are no laws in place to protect you
According to new Snowden documents, the NSA collects over 55,000 “facial recognition quality images” a day through global surveillance programs. That means that in addition to your written and spoken communications and your whereabouts, they’re grabbing your face, too.
The images comes from e-mails, texts, social media, videoconferencing and more.
Via the New York Times:
“It’s not just the traditional communications we’re after: It’s taking a full-arsenal approach that digitally exploits the clues a target leaves behind in their regular activities on the net to compile biographic and biometric information” that can help “implement precision targeting,” noted a 2010 document.
One N.S.A. PowerPoint presentation from 2011, for example, displays several photographs of an unidentified man — sometimes bearded, other times clean-shaven — in different settings, along with more than two dozen data points about him. These include whether he was on the Transportation Security Administration no-fly list, his passport and visa status, known associates or suspected terrorist ties, and comments made about him by informants to American intelligence agencies.
According to the Times, federal privacy and surveillance laws provide no protections for facial images; however, the NSA would, in theory, need court approval to get imagery of Americans. But it’s unclear whether this is honored. (Senator Al Franken is quoted in the Times article as saying “Unfortunately, our privacy laws provide no express protections for facial recognition data.”)
nMeanwhile, law enforcement at the state and local level are also scraping images from driver’s licenses and Facebook to ID suspects; the FBI is working on combining the culled face with fingerprint and biometric data. The State Department and Department of Homeland Security are working on related technologies.
It’s yet another way in which Snowden’s leaks have revealed that the accelerating curve of technology is fast outstripping the legal protections and ethical frameworks that the United States has codified into law—another case of technology working far, far faster than the glacial legal process can. (In much the same way that gun control advocates argue that, for instance, the 2nd amendment couldn’t foresee commercially available AR-15s and school shootings, whether one agrees with them or not.) There’s simply no way that political models laid down in the wake of the Enlightenment could possibly prepare coror protect us from the brutal realities that communications technology is making possible for those who can exploit it outside of the framework of law—i.e. the intelligence community.
It also confirms, perhaps, what I’ve long suspected about surveillance culture. By the early 00s there was literally nowhere in London you could go that you weren’t on CCTV—taking the lead in the creation of a surveillance state, the United Kingdom covered their relatively small land mass with security cameras because it was economically feasible. There’s no way you could do that in the United States; the landmass is just too gigantic and chaotically organized. The answer? Turn the mobile phones and computers into surveillance devices, and introduce social networks to induce people into volunteering their data. In 2008, I sounded like a conspiracy theorist. Now, post-Snowden, we know how much worse, how much more sickeningly worse, the situation really is.
(For a deeper dive: Our Biometric Future: Facial Recognition Technology and the Culture of Surveillance)
(Image via.)
Snowden Selfie Shows You Can Fight the Man and Win (5/22/2014)

Edward Snowden beaming in group selfie with Greenwald, Miranda, Poitras. Why’s he so happy?
Edward Snowden, journalist Glenn Greenwald, Greenwald’s husband David Miranda and filmmaker Laura Poitras pose for a group selfie in Moscow, below, as tweeted by Greenwald’s new media venture The Intercept.
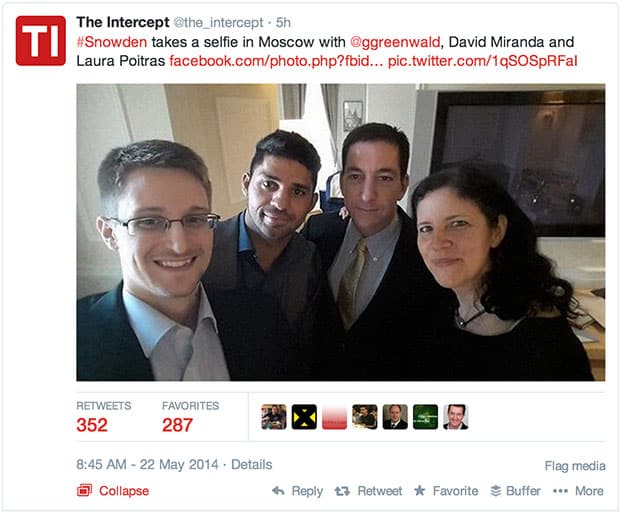
Snowden (despite apparently having only one outfit) looks radiant. As Greenwald said about the whistleblower in a recent interview:
“Of all the people I know in my life, the one who is most at peace and most fulfilled and probably the happiest is Edward Snowden… Because he told me recently, he gets to put his head on his pillow every night knowing that he took actions in defense of this principles.”
Via Al Jazeera:
Greenwald said he continues to correspond with Snowden on a regular basis and described how Snowden, whom the United States has deemed a fugitive, is living his life in Russia under temporary asylum.
“He spends a lot of time following the debate around the world that is unfolding and the reform movements that take place,” Greenwald said. “He’s always been a person of the Internet, spending a lot of time indoors, online. And essentially, he continues to do that.”
Glenn Greenwald’s book on the Snowden saga—No Place to Hide: Edward Snowden, the NSA and the US Surveillance State—is available now.
Glenn Greenwald Names the 5 Americans Targeted by NSA Surveillance (7/9/2014)

A new investigation published today by The Intercept reveals the five Muslim-American leaders targeted by NSA surveillance
(This article written by Ultraculture contributor Andrei Burke.)
Glenn Greenwald has revealed the names of five prominent Muslim Americans whose emails were covertly monitored by the NSA and FBI under procedures intended to target terrorists and foreign spies.
The list, which has been hotly anticipated since it was teased by Greenwald back in May, includes a GOP political candidate along with civil rights activists, academics and lawyers. It was published in an article co-authored by Greenwald and Murtaza Hussain at The Intercept. The list includes:
Faisal Gill, a longtime Republican Party operative and one-time candidate for the Virginia House of Delegates who held top-security clearance and served in the Department of Homeland Security under President George W. Bush;
Asim Ghafoor, a prominent defense attorney who represents clients in terrorism-related cases;
Agha Saeed, former political science professor at California State University East Bay and a champion of civil liberties for Muslims and rights for Palestinians;
Hooshang Amirhamadi, Iranian-American professor of international relations at Rutgers University;
Nihad Awad, executive director of the Council on American-Islamic Relations (CAIR), the largest organization for Muslim civil rights in the country.
The individuals’ names appear on a list in a NSA spreadsheet in the Snowden archives under the title “FISA recap”—an acronym for Foreign Intelligence Surveillance Act. Under this law, the Justice Department needs to convince a judge with the top-secret Foreign Intelligence Surveillance Court that there is probable cause to believe American targets are not only agents of an international terrorist organization or other foreign power, but also “are or may be” engaged in or abetting acts of espionage, sabotage or terrorism. These authorizations are required to be renewed by the court every 90 days for US citizens.
More than 7,000 email addresses are listed that were monitored between 2002 and 2008. Many of the email addresses appear to belong to foreigners whom the government believes are linked to organizations such as Al Qaeda, Hamas, and Hezbollah. Among Americans listed are individuals long accused of terrorist activity, such as Anwar al-Awlaki and Samir Khan, who were both killed in a 2011 drone strike in Yemen.
But Greenwald and Hussain’s investigation reveals that the system for authorizing NSA surveillance affords the government wide latitude in spying on U.S. citizens.
The five Americans whose e-mail accounts were monitored by the NSA and FBI are exemplars of public life and the common good. All five of them vehemently deny any involvement in terrorism or espionage. None advocates violent jihad, neither have they been implicated in a single crime. But all five individuals share one common link: like most of the people listed in the NSA spreadsheet, they are of Muslim heritage.
“I believe that they tapped me because my name is Asim Abdur Rahman Ghafoor, my parents are from India, I travelled to Saudi Arabia as a young man, and I do the pilgrimage,” said Ghafoor after he was told that there was not a single non-Muslim attorney who defended terror suspects that had been identified on the list. “Yes, absolutely I believe that had something to do with it.”
Greenwald, in an interview with Wired, remarked on the significance of this leak, especially as it pertains to how the US treats its Muslim citizens:
“This is the first time that there’s a human face on who the targets are of [the U.S. government’s] most intrusive type of surveillance. It’s all been… sort of abstract… But here you really get to see who these people are who… are worthy of [the] most invasive scrutiny. I think it’s important for people to judge—are these really terrorists or are these people who seem to be targeted for their political dissidence and their political activism?
“Secondly, I think there’s a huge discrepancy between how American Muslims are treated and how non-Muslims are treated. Because there are so many similarly situated non-Muslims who have done as much, if not more, to end up on the list [but] who aren’t on the list. But people who are Muslim end up on the list… and the question becomes, if you’re engaging in political dissidence that some people consider threatening, should you really be targeted?”
While this story will be a major for anyone who has been following the Snowden links since June of last year and/or the government’s treatment of Muslim Americans, don’t expect to find it on the front page of Reddit.
The social media site’s forum for world news (the subreddit called /r/worldnews) is one of the site’s defaults, and has nearly 6 million readers. But the mods at /r/worldnews have a policy of filtering any story from Greenwald’s The Intercept as “opinion.”
During an AMA with Greenwald and Hussain earlier today, Greenwald remarked on the censorship, drawing attention to the mods’ desire to turn the subreddit into a P.R. firm for the Obama administration:
“Reddit is practicing censorship, pure and simple.
“From the comments I’ve seen from the responsible moderators, the people doing this are partisan Democrats who want to conceal these stories because they perceive that it reflects poorly on Obama.
“The reporting we have done has won the Pulitzer, the Polk, and basically every other news reporting prize in the west.
Only on Reddit are our stories deemed something other than ‘news.’
“It’s pitiful.”
Hear that, Reddit? A Pulitzer Prize-winning journalist, with arguably the biggest story on public corruption since Watergate, thinks you’re pitiful.
(Image via.)
NSA Surveillance Harms American Journalism, Law, Economy (7/31/2014)

NSA surveillance programs have already caused significant harm to journalism, law, economy and foreign policy. Will the revised USA Freedom Act provide a solution?
(This article by Ultraculture contributor Andrei Burke.)
Two separate reports released this week detail the harm done by the NSA surveillance dragnet to the American economy, journalism and justice system. Both reports come in the same week that the revised USA Freedom Act was introduced to Congress.
The ACLU and Human Rights Watch published the first of these reports. Titled With Liberty to Monitor All: How Large-Scale US Surveillance is Harming Journalism, Law and American Democracy, the report is the result of interviews with 92 lawyers and journalists. It is filled with detailed evidence of the very real harms done to American journalism and law by NSA surveillance programs.
Some of the most damaging effects from NSA surveillance come from the threat to confidentiality. Journalists cannot promise the same degree of protection to sources’ privacy as they once had, and attorneys fear that their clients may not be providing them with complete information, thus impeding their ability to provide proper counsel. Some journalists have reported resorting to spy tactics to protect a source’s privacy, with Brian Ross of ABC News comparing the paranoid conditions to those of “drug dealers.”
Alex Sinha, the author of With Liberty to Monitor All, told Democracy Now,
I had many attorneys talk about how they feel obligated to warn their clients that their communications are not actually confidential, that there’s a chance that somebody could pick up what they’re saying, and therefore that in order to build their case strategy or in order to exchange basic facts about their case, they need to meet in person, they need to do it in a certain way that’s secure. The journalists reported similar things, that instead of using conventional methods of connecting to sources—emails, phone calls, whatever—you have to contrive a way to bump into a person, you know, meet them face to face, find a way to do that without leaving an electronic trail to set up the meeting in the first place, and which is really slowing down the reporters.
In the same coverage, The Intercept’s Jeremy Scahill declared that there is a “war on journalism,” stating, “In some countries it comes in the form of journalists being murdered. Here, it comes in the form of our communications being surveilled, phone records being seized, our communications being monitored.” Scahill also recalled James Rosen, the Fox News reporter whose private Gmail account was monitored by the Justice Department based on warrants that said he was “co-conspirator” with his source.
The nonpartisan think tank New America Foundation released the other report, titled Surveillance Costs: The NSA’s Impact on the Economy, Internet Freedom & Cybersecurity. This report attempted to quantify and categorize the cost of NSA surveillance programs since The Guardian reported the initial Snowden leaks in June 2013. It contains findings that indicate the NSA’s actions have already caused significant damage to the interests of the US economy and the global Internet community.
Among the findings of Surveillance Costs are direct costs to American businesses, who report declining overseas sales and many lost business opportunities as foreign companies turn claims of products that can protect users from NSA spying into a competitive advantage. According to the report, NSA surveillance has also damaged US foreign policy interests, as has already been witnessed in Germany and Brazil. It also found that NSA surveillance has done serious damage to Internet security through its weakening of key encryption standards.
Both of these reports arrived a day before Senator Patrick Leahy (D-VT) introduced the revised USA Freedom Act to Congress. The measure would end the NSA’s bulk phone records collection and impose new transparency requirements on the intelligence community.
“If enacted, this bill would represent the most significant reform of government surveillance authorities since Congress passed the USA PATRIOT Act 13 years ago,” Leahy said in a Speech on the Senate floor. “This is an historic opportunity.”
Privacy groups have welcomed the bill with caution.
“While this bill is not perfect, it is the beginning of the real NSA surveillance reform that the public has been craving since the Patriot Act became law in 2001,” said ACLU Legislative Director Laura Murphy.
Julian Assange’s Health is Failing (8/19/2014)

WikiLeaks founder Julian Assange is experiencing heart and lung problems, and has announced that he plans to soon leave Ecuador’s embassy in London after having lived there for two years.
(This article by Ultraculture contributor Andrei Burke.)
Wikileaks founder Julian Assange announced that he plans to leave the Ecuadorian embassy in London after having spent the last two years living there to avoid extradition to Sweden over allegations of sexual assault. At a news conference on Monday, Assange told reporters that he would be “leaving the embassy soon,” but for reasons that will not be “reported by the Murdoch press,” without providing further elaboration.
British media reported over the weekend that Assange has been suffering from a laundry list of health problems, including the potentially life threatening heart condition arrhythmia, dangerously high blood pressure and a chronic lung complaint. When asked about his health, Assange replied that anyone would be affected by spending two years in a building with no outside areas or direct sunlight—a complaint he has voiced before. Britain has refused to grant Assange safe passage out of the embassy so that he can travel to Ecuador, in spite of the fact that the South American country had granted him refugee status. Assange did not provide the exact timing or circumstances of his exit.
Kristinn Hrafnsson, a Wikileaks spokesperson, later explained that Assange’s remarks had been “a declaration of hope rather than a declaration that he would be walking out of the embassy.” Hrafnsson said that Assange would leave the embassy when British authorities “grant him safe passage to the airport and to Ecuador.” Assange cited recent changes to British law that could protect him from extradition because charges in Sweden have not yet been filed. But a spokesperson for the Home Office said that the legal changes would not be retroactive and that Assange had “exhausted all appeal avenues.”
“We are clear that our laws must be followed and that Mr. Assange should be extradited to Sweden,” the spokesperson said.
XRay: Incredible Tool Shows Who’s Using Your Data (8/20/2014)
“What are ‘They’ doing with our data?” XRay is a potent new transparency tool that both asks and answers this question
Ever wondered why, exactly, you get specific ads targeted to you as you surf the Web—on Facebook, Gmail, Amazon or anywhere else? The way that advertisers collect and implement your data has largely been kept opaque—until now, that is.
XRay, developed at Columbia Engineering, is a powerful new tool that reveals what data in your web account is being used to target you. Currently in demo, XRay will reveal targeting for Gmail ads, Amazon and YouTube recommendations. As the software progresses, it should be able to provide you with a full profile of exactly who’s harvesting your data, and what they’re doing with it. It’s exactly the kind of tool for radical transparency that we need more of.
Via XRay’s page:
The Web can be a black box. When a user sees an ad about spiritual meditation methods, she may not realize that she’s seeing that ad because she recently received an email about depression or cancer. We are seeking to change that, and in doing so bring more transparency to the Web.
For this, we developed XRay, a new tool that reveals which data in a web account, such as emails, searches, or viewed products, are being used to target which outputs, such as ads, recommended products, or prices. It can increase end-user awareness about what the services they use do with their data, and it can enable auditors and watchdogs with the necessary tools to keep the Web in check.
Currently, XRay can reveal some forms of targeting for Gmail ads, Amazon product recommendations, and YouTube video recommendations. However, XRay’s core mechanisms are largely service-agnostic, providing the necessary building blocks that we hope will enable a new generation of auditing tools that will help lift the curtain on how users’ personal data is being used.
US Court Renews NSA Surveillance Program (9/15/2014)

A federal court renewed an order allowing the NSA to collect phone records for virtually all calls made within the United States
(This article by Ultraculture contributor Andrei Burke.)
Last Friday, a United States federal court renewed an order that allows the National Security Agency (NSA) to collect phone records on nearly all calls made within the country.
The Foreign Intelligence Surveillance Court (FISC) approved the Justice Department’s request for another 90-day extension of the NSA surveillance program, pushing the expiration date back to December 5. The NSA’s controversial program was first exposed last summer by Edward Snowden and is authorized under Section 215 of the Patriot Act.
“Given that legislation has not yet been enacted, and given the importance of maintaining the capabilities of the Section 215 telephony metadata program, the government has sought a 90-day reauthorization of the existing program, as modified by the changes the president announced in January,” the Justice Department and Office of the Director of National Intelligence said in a joint statement.
This extension is the third of its kind since January, when President Obama pledged to reform how the NSA spies on American citizens. Obama outlined a series of immediate steps that would be taken to reform NSA surveillance and enhance transparency, but noted he was waiting for Congress to deliver a him a bill to sign before ending the bulk collection of U.S. phone data.
But Capitol Hill has been slow on NSA surveillance reform this year. As a result the courts have been able to renew the collection of telephone metadata—phone numbers and time stamps of a call but not the actual content—in March, June and now September.
In July, Senate Judiciary Chairman Patrick Leahy (D-VT) introduced the USA Freedom Act, which would effectively end the government’s collection and storage of metadata. It would require that records be retained by phone companies, which intelligence agencies could obtain only after acquiring court approval.
“Congress must ensure that this is the last time the government requests and the court approves the bulk collection of Americans’ records,” Leahy said in a statement. “This announcement underscores, once again, that it is time for Congress to enact meaningful reforms to protect individual privacy.”
The CIA Just Released a Treasure Trove of Documents (9/25/2014)
The CIA recently released more than 250 issues of their internal newsletter under the Freedom of Information Act. Here’s four of the weirder ones.
(This article by Ultraculture contributor Andrei Burke.)
Jeffrey Scudder was a veteran information technology specialist at the Central Intelligence Agency when, in 2007, he discovered the archives of the agency’s in-house newsletter Studies in Intelligence. However, the documents were classified, so Scudder filed a Freedom of Information Act request.
At this point, everything went to hell. A Washington Post profile on Scudder reads:
His request set in motion a harrowing sequence. He was confronted by supervisors and accused of mishandling classified information while assembling his FOIA request. His house was raided by the FBI and his family’s computers seized. Stripped of his job and his security clearance, Scudder said he agreed to retire last year after being told that if he refused, he risked losing much of his pension.
In response to a lawsuit filed by Scudder, the agency declassified and posted nearly 250 journal articles on their website. The declassified articles reveal the strange and surreal inner world of the agency and its employees.
Below are four of the more bizarre ones:
1. “How We Are Perceived”
“It came as a shock to learn that there seem still to be large numbers of well read and presumably intelligent US citizens who perceive that we are assassins, blackmailers, exploiters of sex and illicit drugs as well as the creators of our own foreign policy separate and distinct from that of the Department of State,” wrote an anonymous service member in this 1986 essay. “How can it be that perceptions differ so radically from reality?
The essay alleges that leaks to the press coupled with “some of our acknowledged missteps” fed a trail of Soviet propaganda which eventually led to a misinformed American public. The State Department itself, along with military intelligence, harbored “misperceptions” about the CIA.
“We have the option of keeping mum and allowing the misperceptions to grow, or of tackling them head-on. We have only ourselves to blame if we do nothing to set the record straight,” the essay reads. Apparently, not much has been done to “set the record straight.”
Doesn’t this read like a sociopathic ex-boyfriend wondering with a straight face why none of his ex-girlfriends will speak to him anymore after he put nude photos of them all over the Internet?
2. Leo Theremin—CIA Nemesis
Theremin was best known as the inventor of the eponymous instrument that was a staple of science fiction B-movies of the 50’s. An early pioneer of electronic music, Theremin was also a Soviet spy. He survived the gulag and became a KGB researcher. His “very existence was a state secret.” His greatest coup was placing a bug inside a wooden replica of the Great Seal of the United States that was given to the American ambassador in Moscow in 1945. The hidden microphone wasn’t discovered until 1960.
3. “An Interview With NSA Director Lt. Gen. Michael V. Hayden”
In this pre-9/11 and pre-Snowden era, then-NSA director and future CIA director spoke of this agency’s reputation for extreme secrecy:
Everything’s secret. I mean, I got an e-mail saying, “Merry Christmas.” It carried a Top Secret NSA classification marking. The easy option is to classify everything. This is an Agency that for most of its existence was well served by not having a public image. When the nation felt its existence was threatened, it was willing to cut agencies like NSA quite a bit of slack. But as that threat perception decreases, there is a natural tendency to say, “Now, tell me again what those guys do?” And, therefore, the absence of a public image seems to be less useful today than it was 25 years ago. I don’t think we can survive without a public image.
When asked about the cooperation between intelligence agencies, his answer eerily foreshadowed the intelligence failures behind 9/11 and the ensuing hunt for Osama bin Laden:
Without getting too much into some really sensitive stuff, let’s think about conducting operations against a major international terrorist leader…Think about two agencies, for illustrative purposes, 35 miles apart, trying to marry the data to get the son of a gun. And each of them saying, “I’ll give you my finished reporting, but not my tickets.” You cannot tell me that’s the correct approach in the first year of the 21st century. We’re like two foreign potentates, negotiating a transfer of prisoners, and we’re both wrapping ourselves around our own tradecraft.
4. “Interview with Erna Flegel”
Future CIA chief Richard Helms spoke with a nurse who was stationed in Adolf Hitler’s bunker in Berlin as Nazi Germany collapsed in 1945. Flegel was a “fanatical admirer” of her former employer, and gushed, “When Hitler was in the room, he filled it entirely with his personality—you saw only him, aside from him nothing else existed. The fascinating thing about him was his eyes; up to the end, it was impossible to turn away from his eyes.”
Your Voice is Going to Be Used to Track You (10/13/2014)
Voice biometrics—the use of voice-recognition software to record and use your speech patterns as a unique “fingerprint” that can be used to identify you—will be increasingly standardized for government and businesses in the next two to three years
Everybody has a unique voice—and it can now be used to track you.
That’s the burgeoning field of “voice biometrics,” and businesses and governments are increasingly using the technology to track individuals—an estimated 65 million voiceprints are now in corporate and government databases, according to the Associated Press. And the technology is now widely available, and spreading rapidly.
Among the companies that AP identifies as using biometrics are Barclays Bank, mutual fund manager Vanguard Group, and Turkish cell phone provider Turkcell. On the government side, US law enforcement uses voice biometrics to track inmates and paroled offenders, the Internal Revenue Department in New Zealand currently has 1 million voiceprints on record, and South Africa’s Social Security Agency has tallied 7 million voiceprints.
Via AP:
Activists worry that the popularity of voiceprinting has a downside.
“It’s more mass surveillance,” said Sadhbh McCarthy, an Irish privacy researcher. “The next thing you know, that will be given to border guards, and you’ll need to speak into a microphone when you get back from vacation.”
The legality of voice recording differs from country to country. In the United States, voice recording falls under state, rather than federal law, and rules differ from state to state. In 38 states and the District of Columbia, “conversations may be recorded if the person is party to the conversation, or if at least one of the people who are party to the conversation have given a third party consent to record the conversation. In California, Connecticut, Delaware, Florida, Illinois, Maryland, Massachusetts, Nevada, New Hampshire, Pennsylvania, Vermont, and Washington State, the consent of all parties of the conversation must be obtained in order to record a conversation,” according to Wikipedia.
Consent, of course, may be given without much thought—it might easily be buried in, for instance, a phone company’s terms of service, or an “all calls may be recorded for training purposes” notice on a phone call you sleep through.
Within the next two to three years, it’s expected that more and more companies will begin standardizing the use of voice biometrics as passwords—you’ll just speak your name or a phrase into the phone to identify yourself, instead of a password.
Of course, once locked in, voice biometrics could conceivably be used to track individuals in public places, meaning that the use of cell phones to monitor and track individuals could be obsolete, giving way to simply tracking any spoken word as long as it’s in the range of equipment sensitive enough to identify voice biometrics.
The Electronic Frontier Foundation has been sounding the alarm about biometrics and civil liberties violations since 2003—in this case, facial recognition technology. Documents released by Edward Snowden this summer reveal that NSA surveillance programs collect over 55,000 facial recognition quality images a day through global NSA surveillance programs—through e-mails, texts, social media, videoconferencing and more. As the NSA has been demonstrated to track and record nearly all cell phone calls, it presumably wouldn’t be much trouble to use that information for establishing a covert voice biometrics database.
Watch what you say—anywhere.
(Image via Wikimedia Commons.)
United Nations Report Finds Mass Surveillance is ‘Corrosive’ (10/16/2014)

The United Nations Special Rapporteur finds that mass surveillance is “indiscriminately corrosive of online privacy”
Glenn Greenwald reports that the the United Nations Special Rapporteur (their top counterterrorism and human rights official) has given a formal report to the United Nations General Assembly that mass surveillance violates international privacy rights, and argued that “Bulk access technology is indiscriminately corrosive of online privacy… in the absence of a formal derogation from States’ obligations under the Covenant, these programs pose a direct and ongoing challenge to an established norm of international law.”
Via the Intercept:
Central to the Rapporteur’s findings is the distinction between “targeted surveillance” — which “depend[s] upon the existence of prior suspicion of the targeted individual or organization” — and “mass surveillance,” whereby “states with high levels of Internet penetration can [] gain access to the telephone and e-mail content of an effectively unlimited number of users and maintain an overview of Internet activity associated with particular websites.” In a system of “mass surveillance,” the report explained, “all of this is possible without any prior suspicion related to a specific individual or organization. The communications of literally every Internet user are potentially open for inspection by intelligence and law enforcement agencies in the States concerned.”
Mass surveillance thus “amounts to a systematic interference with the right to respect for the privacy of communications,” it declared. As a result, “it is incompatible with existing concepts of privacy for States to collect all communications or metadata all the time indiscriminately.”
Watch a Brand New, Fascinating Edward Snowden Interview (10/27/2014)

Excellent new Edward Snowden interview, conducted via satellite by legal activist Lawrence Lessig at Harvard Law School
(This article by Ultraculture contributor Andrei Burke.)
Check out the video below to see Lawrence Lessig interview Edward Snowden via satellite at the Harvard Law School on October 20.
In the hour-long interview, Snowden discusses his background, his motives for the massive NSA surveillance leak in July 2013, the duty of the press, and more.
Lawrence Lessig is director of the Edmond J. Safra Center for Ethics at Harvard University and a Professor of Law at Harvard Law School, an activist and scholar of constitutional law. He’s fought to reduce draconian legal restrictions on copyright, trademark and radio frequency–and to adapt those laws to the demands of the information age. He wrote about communications technology and copyright law in the books Code and Other Laws of Cyberspace, The Future of Ideas and Free Culture. Lessig has recently turned his fight to the problem of big money in politics. In May, he founded the May Day PAC in order to elect candidates to Congress who would pass campaign finance reform.
Edward Snowden is the subject of filmmaker Laura Poitras’ recent documentary Citizenfour, which details the time leading up to and following Snowden’s historical NSA surveillance leaks to Glenn Greenwald in July 2013 and his exile in Moscow since.
Major Victory Against Mass GCHQ and NSA Surveillance (2/6/2015)

British court declares that the GCHQ’s collection of data from the NSA was illegal
A British court—the Investigatory Powers Tribunal—ruled today that the GCHQ (Government Communications Headquarters), the UK equivalent of the NSA, was acting unlawfully and violating human rights when it used data provided by the NSA, because it didn’t make its safeguards public. The legal challenge was brought by Privacy International, Amnesty International and other civil liberty organizations.
The IPT’s ruling, found here, states:
(i) THAT prior to the disclosures made and referred to in the First Judgment and the Second Judgment, the regime governing the soliciting, receiving, storing and transmitting by UK authorities of private communications of individuals located in the UK, which have been obtained by US authorities pursuant to Prism and/or (on the Claimants’ case) Upstream, contravened Articles 8 or 10 ECHR, but
(ii) THAT it now complies with the said Articles.
As the safeguards governing GCHQ exchanges with the NSA’s PRISM and UPSTREAM programs were made public in December, the program is now lawful—and has not stopped. The GCHQ, in fact, publicly thanked the IPT, stating “We are pleased that the court has once again ruled that the U.K.’s bulk interception regime is fully lawful.”
Yes, that’s an actual quote. “Bulk interception regime.”
He added: “Today’s IPT ruling re-affirms that the processes and safeguards within the intelligence-sharing regime were fully adequate at all times – it is simply about the amount of detail about those processes and safeguards that needed to be in the public domain. We welcome the important role the IPT has played in ensuring that the public regime is sufficiently detailed.”
Despite this grim response from the GCHQ, the ruling is still a major victory, as it sets a precedent keeping mass surveillance programs public knowledge instead of clandestine operations. The civil liberty groups who brought the challenge will appeal the lawfulness of the current system to the European Court of Human Rights.
And next, the NSA?
(h/t Washington Post)
(Image via.)
Disturbing: Samsung’s SmartTV records you while you watch (2/9/2015)

Samsung’s new SmartTV records the voices of its viewers and transmits them to a third party for storage. Is this the start of disturbing new trend in consumer electronics?
Samsung’s Internet-connected SmartTV has a disturbing new feature: It records everything around it and sends it back to a third party service that converts speech to text. That’s a feature that not only presents a disturbing violation of privacy, but also could be hijacked by other parties—even hackers.
A single sentence buried in a dense “privacy policy” for Samsung’s Internet-connected SmartTV advises users that its nifty voice command feature might capture more than just your request to play the latest episode of Downton Abbey.
“Please be aware that if your spoken words include personal or other sensitive information, that information will be among the data captured and transmitted to a third party,” the policy reads.
So be advised: If you’re too lazy to pick up the remote, you may want to keep your conversation with the TV as direct and non-incriminating as possible. Don’t talk about tax evasion, drug use. And definitely don’t try out your Violet Crawley impression.
Judging by the privacy policy, it seems Samsung is collecting voice commands mostly to improve the TV’s performance. “It looks like they are using a third-party service to convert speech to text, so that’s most of what is being disclosed here,” said Corynne McSherry, the intellectual property director at the Electronic Frontier Foundation.
As with all new surveillance technology, I’m not sure what’s more disturbing—the existence of the technology itself (from SmartTVs to the entire NSA surveillance apparatus) or the American public’s willingness to accept it with barely a second thought.
For more on how to resist electronic spying, please visit the Electronic Frontier Foundation (EFF).
Your Hard Drive is Infested With NSA Surveillance Software (2/17/15)

Western Digital, Seagate, Toshiba and other manufacturers’ hard drives now come loaded with NSA surveillance spyware, according to private security firm Kaspersky Lab
According to Kaspersky Lab (an Internet security firm), a long-running NSA surveillance operation entitled the “Equation Group” is embedding near-invisible spy software in hard drives manufactured by Western Digital, Seagate, Toshiba and others.
The spy software is designed to target military and government institutions, telecommunications and media, banks, energy companies, nuclear researchers and Islamic activists (via); the extent to which hard drive companies cooperated with the NSA is uncertain.
From the Kaspersky report:
For several years, Kaspersky Lab’s Global Research and Analysis Team (GReAT) has been closely monitoring more than 60 advanced threat actors responsible for cyber-attacks worldwide. The team has seen nearly everything, with attacks becoming increasingly complex as more nation-states got involved and tried to arm themselves with the most advanced tools. However, only now Kaspersky Lab’s experts can confirm they have discovered a threat actor that surpasses anything known in terms of complexity and sophistication of techniques, and that has been active for almost two decades – The Equation Group.
According to Kaspersky Lab researchers the group is unique almost in every aspect of their activities: they use tools that are very complicated and expensive to develop, in order to infect victims, retrieve data and hide activity in an outstandingly professional way, and utilize classic spying techniques to deliver malicious payloads to the victims.
To infect their victims, the group uses a powerful arsenal of “implants” (Trojans) including the following that have been named by Kaspersky Lab: EquationLaser, EquationDrug, DoubleFantasy, TripleFantasy, Fanny and GrayFish. Without a doubt there will be other “implants” in existence.
Post-Snowden, it appears that the latest vanguard in watchdogging NSA surveillance is private security firms looking to make a name for themselves and gain clients. Earlier this week, for instance, the company F-Secure uncovered a potential spy feature in Google Chrome.
(Image via.)
The Future of NSA Surveillance
The battle over NSA surveillance is ongoing—and now that all that power is concentrated in the hands of a demagogue like Donald Trump, more critical than ever.
For the latest on where the battle is going, please visit the Electronic Freedom Foundation.